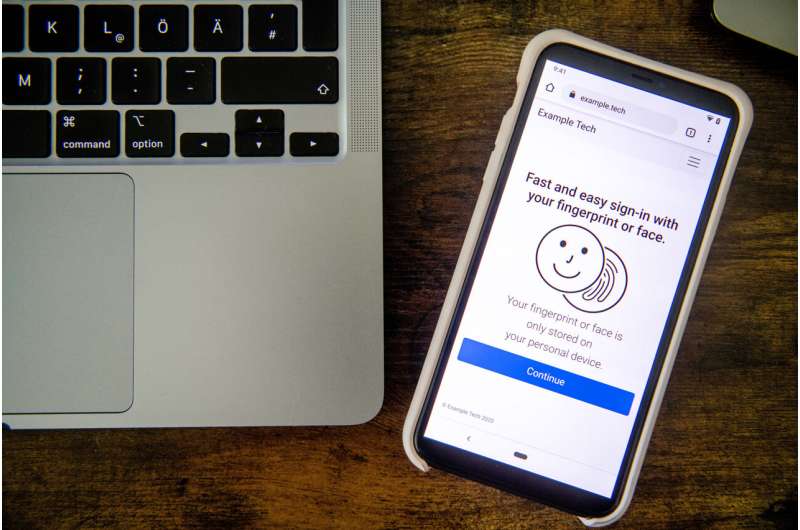
WebAuthn could make passwords obsolete. Credit: RUB, Marquard
Many users consider passwords extremely burdening. An authentication protocol for websites, called WebAuthn, could render them obsolete. Users can use it to log on to a service such as a social network or an online shopping platform with their smartphone or computer. The process is quick and easy when using biometric data such as fingerprint or face recognition, which are often already stored to unlock the device. "It is not surprising that this can create the impression that the biometric data is transmitted to the website to which you want to log in, similar to a password. But this is a misconception," says Leona Lassak from Ruhr-Universität Bochum (RUB).
A team from RUB, the Max Planck Institute for Security and Privacy (MPI-SP) in Bochum and the University of Chicago has been tackling these and other misconceptions. In several online studies, they let 414 users try out the new WebAuthn sign-in and asked them about their first impressions and concerns regarding its security, usability, and privacy.
Leona Lassak from the Horst Görtz Institute for IT Security at RUB and Dr. Maximilian Golla from the MPI-SP, together with Annika Hildebrandt and Professor Blase Ur from the University of Chicago, will publish the results at the USENIX Security conference on 11 August 2021. The paper has been available online since 21 June 2021.
How WebAuthn works
WebAuthn is part of the new FIDO2 standard, which aims at making passwords obsolete. Currently, when users want to log in to a service, they just enter a username and password. In the future, users could instead authenticate themselves simply by using their device. To ensure that a random person who finds a lost smartphone won't be able to sign in to all kinds of services, users have to confirm the login process with their smartphone PIN or biometrics. Some services such as the American eBay or Microsoft already offer the WebAuthn login.
Leona Lassak explains the problem: "For the user it seems like they are logging in to the online service with their fingerprint. In fact, their fingerprint only unlocks a so-called cryptographic key, which is stored on the user's device and is then used for the actual login."
Confusion among first-time users
Nearly 70 percent of respondents were unsure or mistakenly believed that their biometric data would be shared with the website they were trying to sign in. "It is important to address these misunderstandings, as they jeopardize people's willingness to use the new secure sign-in," says Annika Hildebrandt, an author from the University of Chicago.
Another problem arises in case the fingerprint sensor doesn't work. In fact, it is possible to enter the smartphone PIN alternatively. However, since the user interface doesn't make this option very clear, 60 percent of users thought they would lose access to their account in this case. The researchers also asked whether participants would feel their accounts were safe if their smartphone was stolen. 93 percent of respondents felt sufficiently protected due to their biometrics but were unaware that an attacker could also gain access to their accounts by guessing the smartphone PIN.
Addressing misconceptions
The researchers let seven focus groups develop texts and graphics which aim to prevent these misconceptions and communicate the complicated functionality of WebAuthn. Based on these texts, the researchers implemented six notifications and compared them in an online study.
"Most effective in addressing misconceptions, is to communicate explicitly that the fingerprint and face data is never transmitted to the website," explains Annika Hildebrandt. It was less effective to highlight the disadvantages of passwords or to mention the trustworthy companies that helped to develop the WebAuthn standard.
Increasing adoption
Despite all misunderstandings and concerns, participants rated the biometric login higher than traditional passwords, as they were particularly impressed by its speed and ease of use. In the future, the researchers intend to further increase the acceptance of WebAuthn to make its advantages accessible to all users.
More information: It's stored, hopefully, on an encrypted server, www.blaseur.com/papers/fido2bi … metrics-extended.pdf
Provided by Ruhr-Universitaet-Bochum