Credit: Unsplash/CC0 Public Domain
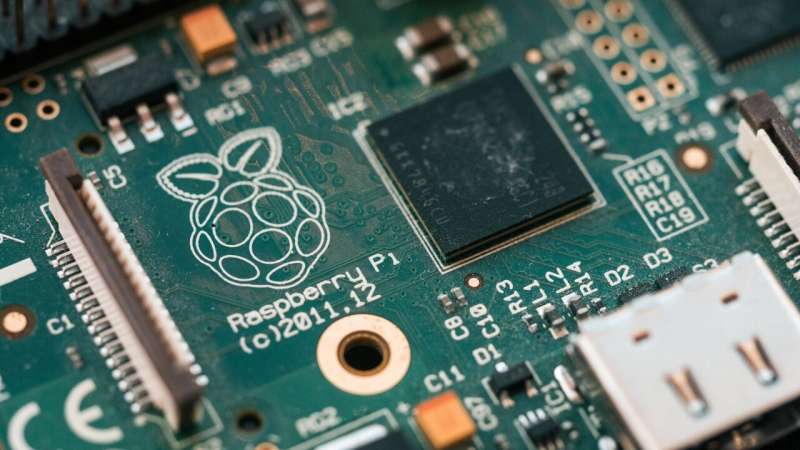
A team of researchers at the Institute of Computer Science and Random Systems has built a non-software-based virus detection system using a Raspberry Pi, an H-field probe and an oscilloscope to detect electromagnetic wave signatures of multiple types of viruses. The team presented its system and test results at last month's ACM Machinery's Annual Computer Security Applications Conference and published a paper describing their system on ACM's Research Article page.
The idea behind the new system is that running software generates electromagnetic waves. And each piece of software generates its own unique wave patterns due to the way the software executes its code. The researchers took advantage of this knowledge and began using an H-field probe to capture wave patterns of known computer viruses running on various devices and viewed the results on an oscilloscope. They saw oscilloscope patterns that were unique to individual viruses as they were running. The researchers used that information to program a Raspberry Pi to identify data from the other two devices to recognize known virus wave patterns, using the system as a virus detector. To determine if a virus is running on a computer, IoT device or smartphone, a user places the H-field probe close enough to the device to read the electromagnetic waves that are generated. The Raspberry Pi then reports on whether it found any viruses, and if so, which ones. Testing found the system capable of detecting 99.82% of generic malware, along with a benign virus type.
The system is notable because it does not require software installation on the device being tested—detection is done using the external system. It is also notable because it is not susceptible to obfuscation techniques developed by the virus builders to hide its presence. Such a system is not likely to be sold to consumers, however, but it could very well be used for large applications or servers.
More information: Duy-Phuc Pham et al, Obfuscation Revealed: Leveraging Electromagnetic Signals for Obfuscated Malware Classification, Annual Computer Security Applications Conference (2021). DOI: 10.1145/3485832.3485894
© 2022 Science X Network